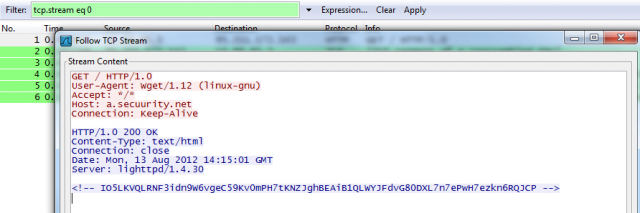
Because of incorrect research contained in the original report, this article previously misidentified a command and control server that was being accessed by computers infected by the Gauss espionage malware. Contrary to that report, the server is operated by researchers with antivirus provider Kaspersky Lab. Such "sinkholes" are used disrupt computer botnets by preventing infected machines from reporting to malicious servers under the control of the malware operator.
Shortly after this article was published, Kaspersky Chief Security Expert Alexander Gostev issued the following statement:
After discovering Gauss we started the process of working with several organizations to investigate the C2 servers with sinkholes. Given Flame's connection with Gauss, the sinkhole process was being organized to monitor both the Flame and Gauss’ C2 infrastructures. It’s important to note that the Gauss C2 infrastructure is completely different than Flame's. The Gauss C2s were shut down in July by its operators and the servers have been in a dormant state by the operators since then. However, we wanted to monitor any activity on both C2 infrastructures.
Read 15 remaining paragraphs | Comments
DIGITAL JUICE
No comments:
Post a Comment
Thank's!